Cyber Forensics - Active Directory Investigation - Cyber Security Blogs - Cyber Forensics - Valency Networks - Best VAPT Penetration Testing Cyber Security Company - Pune Mumbai Hyderabad Delhi Bangalore Ahmedabad Kolkata
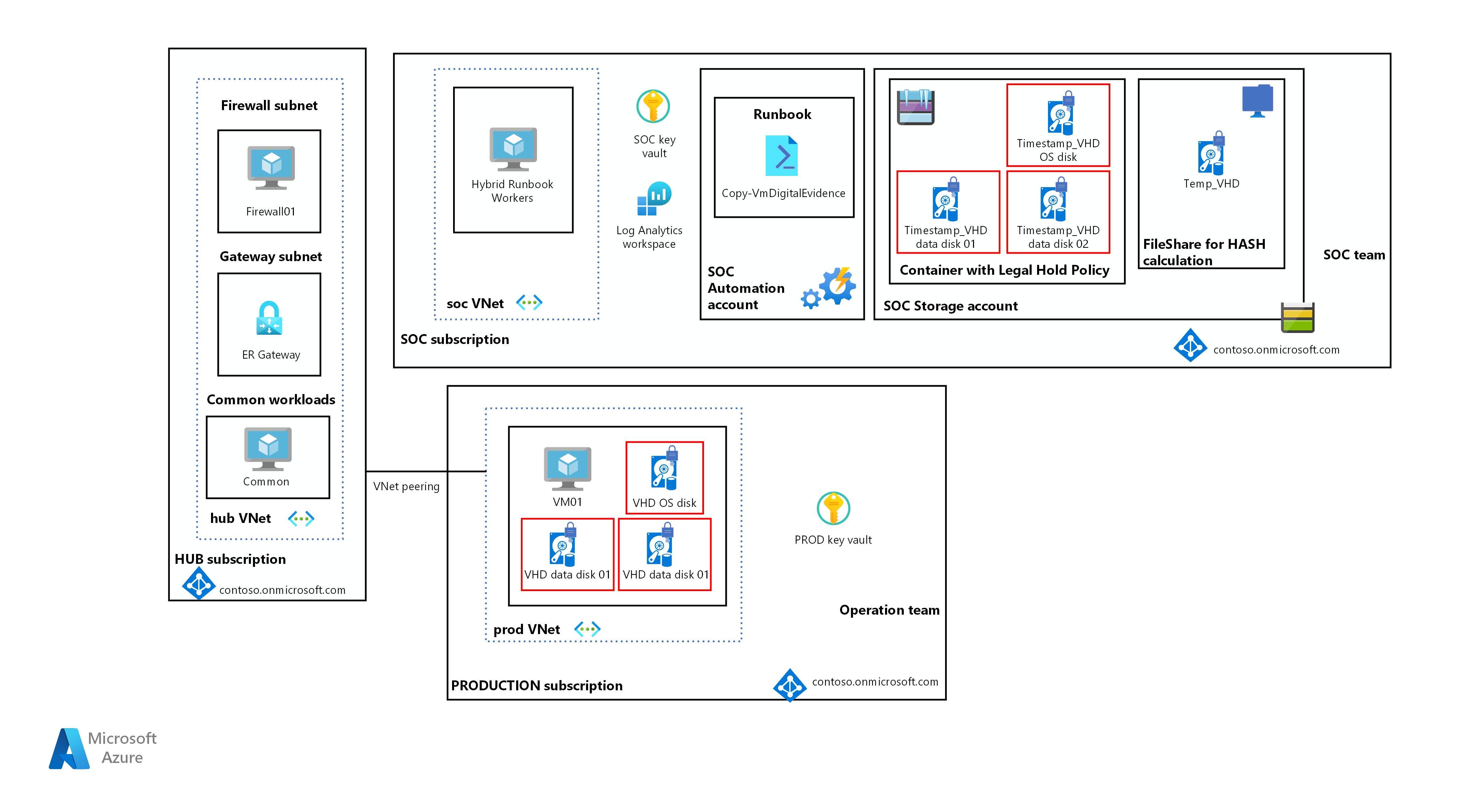
Future Internet | Free Full-Text | Exploiting Misconfiguration Vulnerabilities in Microsoft’s Azure Active Directory for Privilege Escalation Attacks

ADTimeline – Active Directory forensics with replication metadata at the FIRST Technical Colloquium | Agence nationale de la sécurité des systèmes d'information